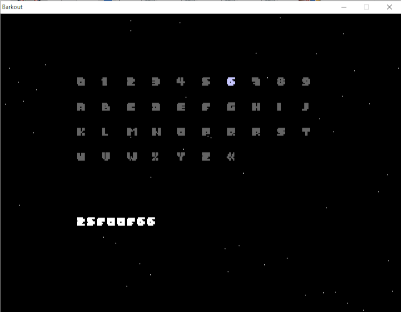
After a few months of not looking at it, I've recently been working on making a few old-school improvements to Barkout, namely a continue code-style save game mechanism, and a new power up in the form of a multi-ball bonus, common in most other Arkanoid clones.
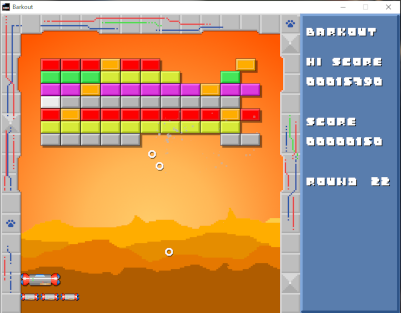
Above, the multi-ball powerup in action.
Below, using the Continue screen to enter a code.
The purpose of Barkout all along has simply been to get some practice in C programming. Initially, it was so I could help a family member who had started a C programming course at university, but it then evolved into doing it just because I enjoyed it. C is a great language to program in. It's also just a nostalgia trip for me; trying to program the sorts of games that I played on my first computer in the 80s: an Amstrad CPC6128.
Anyway, the fruit of my effort is that Barkout version 1.2.0 has now been released and can be found by following the "Free Games!" icon in the top menu.
The musings, struggles and observations of an Englishman learning Welsh.
All Posts
Search Posts
Barkout v1.2.0 Released!
Programming
Posted on 2025-10-17
Comments
